Blog & Resource Hub
Browse all migrated Valydex content in one place. Search by topic, filter by format, and move between guides, reviews, and comparisons without jumping between separate indexes.
Articles

The Best Business Password Manager in 2026
Business password manager comparison for 2026 — verified pricing, feature analysis, compliance mapping, and a clear recommendation for SMBs by team size and budget.
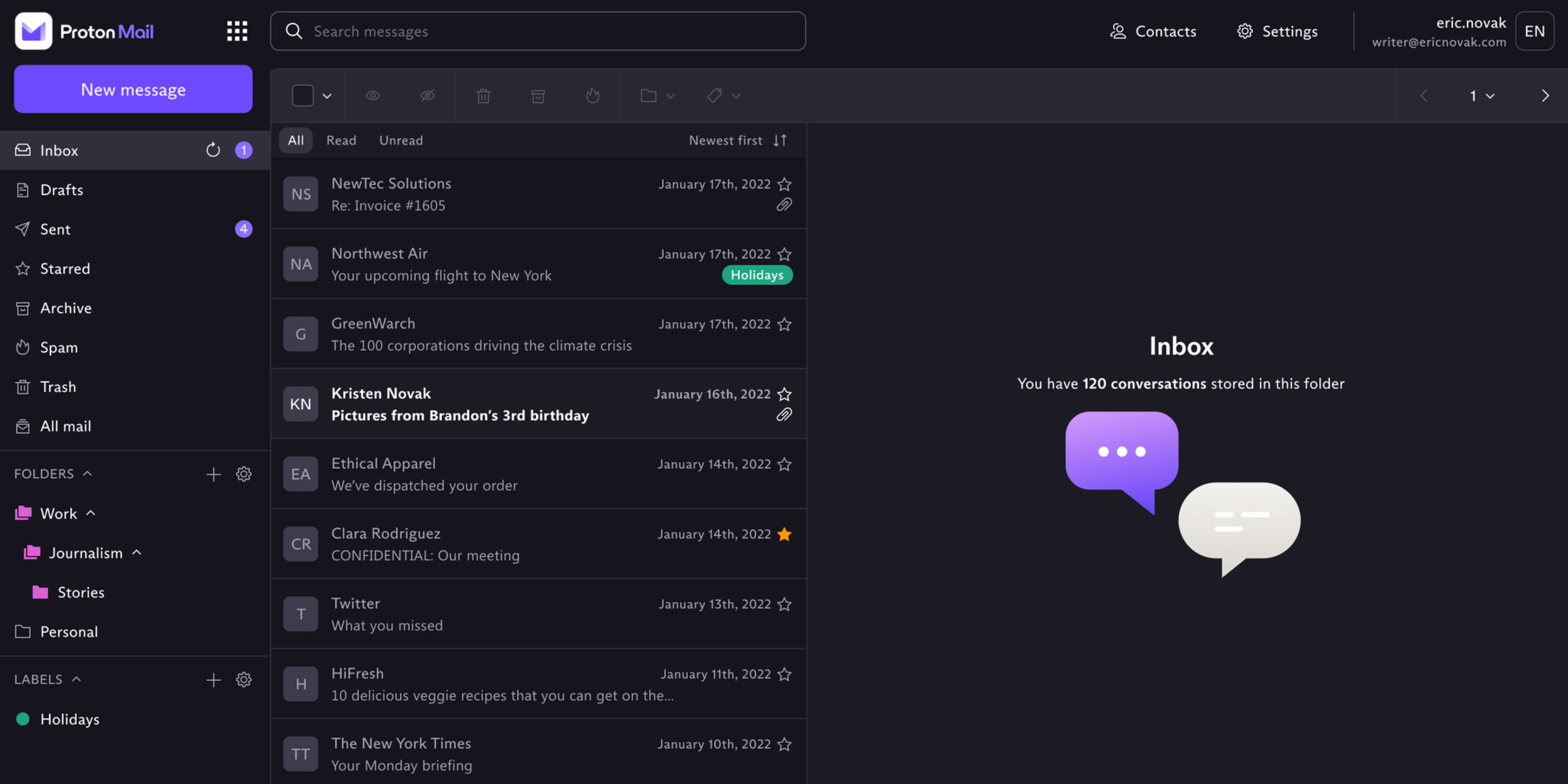
What Proton Business Actually Costs in 2026
Proton Business pricing explained: full tier breakdown, additional costs to consider, and a per-seat comparison against Google Workspace and Microsoft 365.

What Tenable Nessus Actually Costs in 2026: Pricing, Tiers, and Hidden Fees
Current Nessus pricing for every tier: Essentials, Essentials Plus, Professional ($4,790/yr), and Expert ($6,790/yr). Includes hidden costs, the free tier limit, and budget alternatives.

Cybersecurity Toolbox for SMB Teams (2026)
Implementation-focused framework for selecting and operating cybersecurity tools across identity, endpoint, email, backup, and network controls.

Privacy-First Cybersecurity Guide (2026)
A practical implementation guide with NIST-aligned controls, AI-governance safeguards, and a 90-day rollout plan for finance, operations, and IT leaders.

UniFi + Wazuh Security Stack Guide (2026)
Source-backed component choices, pricing signals, integration paths, and deployment tradeoffs for UniFi CyberSecure and Wazuh.

De-Google Your Business Guide (2026)
A comprehensive guide to reducing your organization's dependence on Google services while maintaining productivity, improving data privacy, and strengthening regulatory compliance with alternatives like Proton Business Suite.

Google Workspace to Proton Migration Guide (2026)
Step-by-step migration guide covering planning, technical implementation, common challenges, and post-migration tasks for organizations moving from Google Workspace to Proton with realistic timelines and practical solutions.

Outgrown Consumer VPN? 6 Signs to Move to Business VPN
Implementation guide for identifying when SMB teams should transition from consumer VPN tools to business VPN controls, with cost and migration planning.

Small Business Cybersecurity Guide (2026)
Implementation-first SMB cybersecurity playbook covering baseline controls, governance cadence, and leadership-ready decision frameworks.

Security Tips for Small Business (2026)
Practical security tips designed for recurring cadence—not one-time fixes. Turn best practices into operational controls that survive business pressure.

UniFi IT Solutions Review (2026)
Independent review of UniFi IT solutions covering security controls, deployment tiers, operational tradeoffs, and total cost planning for business environments.

Cybersecurity Predictions 2026 for Small Business
Implementation-focused 2026 outlook for SMB teams, with trend translation, staged roadmap, and governance priorities.

AI-Enhanced BEC Guide (2026)
Implementation-focused guide to AI-enhanced business email compromise, with incident lessons and verification workflows that reduce payment fraud risk.

Business Cyberattack Recovery Checklist (2026)
Step-by-step guide for containing breaches, coordinating response, restoring operations safely, and hardening controls after an incident.

Endpoint Protection Guide (2026)
Comprehensive guide to understanding endpoint protection features for small and medium businesses. Learn about detection technologies, management capabilities, and how to evaluate solutions that match your security needs and budget.

Backup Strategy Considerations for Small Businesses (2026)
Decision-focused backup strategy guide covering data prioritization, 3-2-1 architecture choices, and practical implementation governance for SMB teams.

Password Manager Implementation Guide (2026)
Comprehensive guide covering practical implementation considerations for business password managers, from planning through ongoing management and success measurement.

Cybersecurity Training Guide (2026)
Implementation guide for SMB teams to design, run, and govern cybersecurity training programs that improve decision quality in real workflows.

LogMeIn Pro Review (2026)
Independent analysis of LogMeIn Pro covering security architecture, pricing model, implementation effort, and alternative-fit decisions.

NIST CSF 2.0 Assessment Tool (2026)
Implementation-focused guide for SMB teams using NIST CSF 2.0 profiles, governance, and phased remediation planning.

Ransomware First 30 Minutes Playbook (2026)
Practical crisis checklist for the first 30 minutes of a ransomware incident, including containment, reporting, evidence handling, and controlled recovery setup.

5-Minute Security Wins for Small Business (2026)
Quick-start SMB security guide with high-impact controls you can execute in minutes, then operationalize over 30 days.

Deepfake and AI Manipulation Defense Guide (2026)
Implementation-focused guide for detecting, verifying, and responding to deepfake-driven fraud and manipulation attempts.

Free Cybersecurity Tools for Small Business (2026)
Implementation-first guide to free cybersecurity tools with operational limits, maintenance expectations, and phased upgrade planning.

Action1 Patch Management Review (2026)
Independent analysis of Action1 patch management covering free-tier adoption, operational fit, pricing model, and alternatives for 2026 planning.

KnowBe4 Security Awareness Training Review (2026)
Independent analysis of KnowBe4 covering pricing tiers, rollout requirements, automation depth, and practical alternatives for SMB and mid-market teams.

Microsoft Defender for Office 365 Review (2026)
Independent analysis of Defender for Office 365 covering Plan 1 vs Plan 2 fit, licensing complexity, and practical deployment tradeoffs.
Cisco Umbrella Business Review (2026)
Independent analysis of Cisco Umbrella covering quote-driven pricing, deployment tradeoffs, and operational fit versus common DNS-security alternatives.

Google Password Manager for Business (2026)
Expert analysis of Google Password Manager for business use, covering limitations, ideal scenarios, and detailed comparisons with professional password management solutions including Bitwarden, 1Password, and NordPass.

Service Business Security Guide (2026)
Source-backed guide for securing service businesses across client sites, mobile devices, public networks, and distributed workflows.

Mobile Workforce Security Guide (2026)
Source-backed guide to secure mobile workforce operations with identity, endpoint, connectivity, and governance controls.

AI Cybersecurity Risks for Small Business (2026)
Implementation-first guide to AI security controls for SMB teams, including policy design, monitoring, and response workflows.

AI Cyberattacks and NIST Guide for Small Business (2026)
Implementation-first guide using NIST IR 7621r2 and CSF 2.0 to reduce AI-driven cyber risk in solo and small-team environments.

Cybersecurity Statistics 2025-2026 for Small Business
Implementation-focused analysis translating current cybersecurity trend data into budget, control, and governance actions for SMB teams.

Synology NAS Business Review (2026)
Independent Synology NAS analysis covering platform fit, hardware constraints, pricing reality, and operational deployment planning.

Password Manager Guide For Small Business
Practical password manager guide covering tool selection, rollout planning, policy controls, and adoption strategy for small business teams.

Ransomware Protection Guide (2026)
Source-backed implementation guide for ransomware resilience across identity, endpoint, patching, backup recovery, and incident governance.

NordLayer Business Review (2026)
Independent analysis of NordLayer Business covering architecture, pricing tiers, rollout effort, and competitive fit.

Zero Trust Guide (2026)
Source-backed guide for building a zero trust operating model with phased rollout, governance metrics, and policy-driven access controls.

Network Security Guide (2026)
Source-backed network security implementation guide with policy baselines, 90-day rollout, and governance metrics.

Small Business Cybersecurity Checklist (2026)
A standards-aligned SMB checklist with owner mapping, evidence requirements, and monthly governance cadence.

Endpoint Protection Guide (2026)
Source-backed guide covering endpoint control baselines, tooling decisions, Microsoft Defender pricing signals, incident response, and quarterly governance metrics.

Remote Work Security Guide (2026)
Source-backed remote-work security guide covering secure access, BYOD controls, endpoint policy, and governance.

Cloud Security Guide (2026)
Source-backed cloud security guide covering shared responsibility, identity controls, workload hardening, telemetry, and governance.

Small Business Cybersecurity Roadmap (2026)
Source-backed 90-day roadmap covering identity, endpoint, email, network, backup, incident response, and governance controls.

CrowdStrike Falcon Go Review (2026)
Independent review of CrowdStrike Falcon Go covering detection model, pricing tiers, operational overhead, and practical alternatives.

Email Security Tester Guide (2026)
Privacy-first workflow for validating domain email authentication settings and reducing spoofing and phishing exposure.

Business Email Security Playbook (2026)
Source-backed guide covering sender authentication, mailbox hardening, verification policy, incident response, and quarterly governance metrics.

Spot the Fake: BEC Verification Guide
Learn to identify business email compromise scams using plain-English red flags, a two-step callback policy, and ready-to-use verification templates for your finance team.

Proton VPN Business Review (2026)
Independent review of Proton VPN Business covering pricing tiers, security architecture, rollout complexity, and practical alternatives.

Proton Pass Business Review (2026)
Independent review of Proton Pass Business covering pricing tiers, security architecture, rollout complexity, and ecosystem fit.

NordPass Business Review (2026)
Independent review of NordPass Business covering pricing realities, security architecture, rollout overhead, and practical alternatives.

Cisco Duo MFA Review (2026)
Independent review of Cisco Duo MFA covering free and paid tiers, policy depth, Microsoft comparisons, and rollout reality.

1Password Business Review (2026)
Independent review of 1Password Business covering pricing realities, security architecture, rollout overhead, and practical alternatives.

Small Business Backup Strategy (2026)
Implementation-first backup guide covering architecture choices, restore-governance standards, and cost-aware rollout for small and growing teams.

Cybersecurity on a Budget Guide (2026)
Source-backed budget security guide using phased controls, measurable outcomes, and governance-first spending decisions.

Business Backup Solutions Guide (2026)
Implementation-first backup playbook covering sync-vs-backup decisions, verified pricing signals, RPO/RTO design, and a 90-day rollout model.

Cybersecurity Incident Response Plan (2026)
Source-backed incident response guide covering first-hour actions, role ownership, evidence handling, communications, and governance.

Proton Pass vs 1Password Business (2026)
In-depth comparison of Proton Pass Business and 1Password Business for organizations evaluating password-management platforms.

Business VPN vs Consumer VPN (2026)
Implementation-focused comparison of business VPN and consumer VPN models for SMB teams, including governance requirements and rollout strategy.

Password Manager Comparison for Business (2026)
Implementation-focused comparison of leading business password managers for SMB teams, with decision frameworks and operational tradeoffs.
Box Business Review (2026)
Independent analysis of Box Business covering pricing, compliance posture, implementation effort, and operational fit versus common alternatives.
Malwarebytes ThreatDown Business Review (2026)
Independent review of Malwarebytes ThreatDown Business covering response depth, pricing tiers, rollout overhead, and SMB fit.

Bitwarden Business Review (2026)
Independent review of Bitwarden Business covering trust architecture, rollout considerations, pricing tradeoffs, and alternative fit.

1Password vs Built-in Password Managers (2026)
Implementation-focused comparison of 1Password Business and built-in password tools from Google, Apple, and Microsoft.

Cybersecurity Compliance Guide (2026)
Source-backed compliance guide with a unified control model, evidence strategy, and governance workflow for SMB and mid-market teams.

NordLayer vs Check Point SASE (Perimeter 81) 2026
Detailed comparison of NordLayer and Check Point SASE (formerly Perimeter 81) across pricing structure, support model, compliance fit, and operational complexity.

WiFi 7 Wireless Security Guide (2026)
Practical WiFi 7 deployment guide with WPA3 migration controls, 6GHz security considerations, and phased business rollout planning.
Cisco Umbrella vs Cloudflare (2026)
Comprehensive comparison of Cisco Umbrella and Cloudflare across DNS filtering depth, pricing model, and implementation fit.

Acronis Cyber Protect Review (2026)
Independent review of Acronis Cyber Protect covering backup reliability, integrated security controls, pricing tradeoffs, and implementation considerations for 2026.

NIST CSF 2.0 Implementation Guide (2026)
Source-backed implementation guide with function mapping, profile scoping, a 90-day plan, and quarterly governance metrics.
Microsoft 365 vs Proton Business Suite (2026)
Comprehensive comparison of Microsoft 365 and Proton Business Suite across security model, pricing, compliance, and migration fit.

Google Workspace vs Proton Mail Business (2026)
Compare Google Workspace and Proton for Business across security model, pricing, compliance fit, and migration realities.

Tenable Nessus Review (2026)
Independent Tenable Nessus analysis covering edition fit, pricing model, deployment complexity, and operational alternatives.
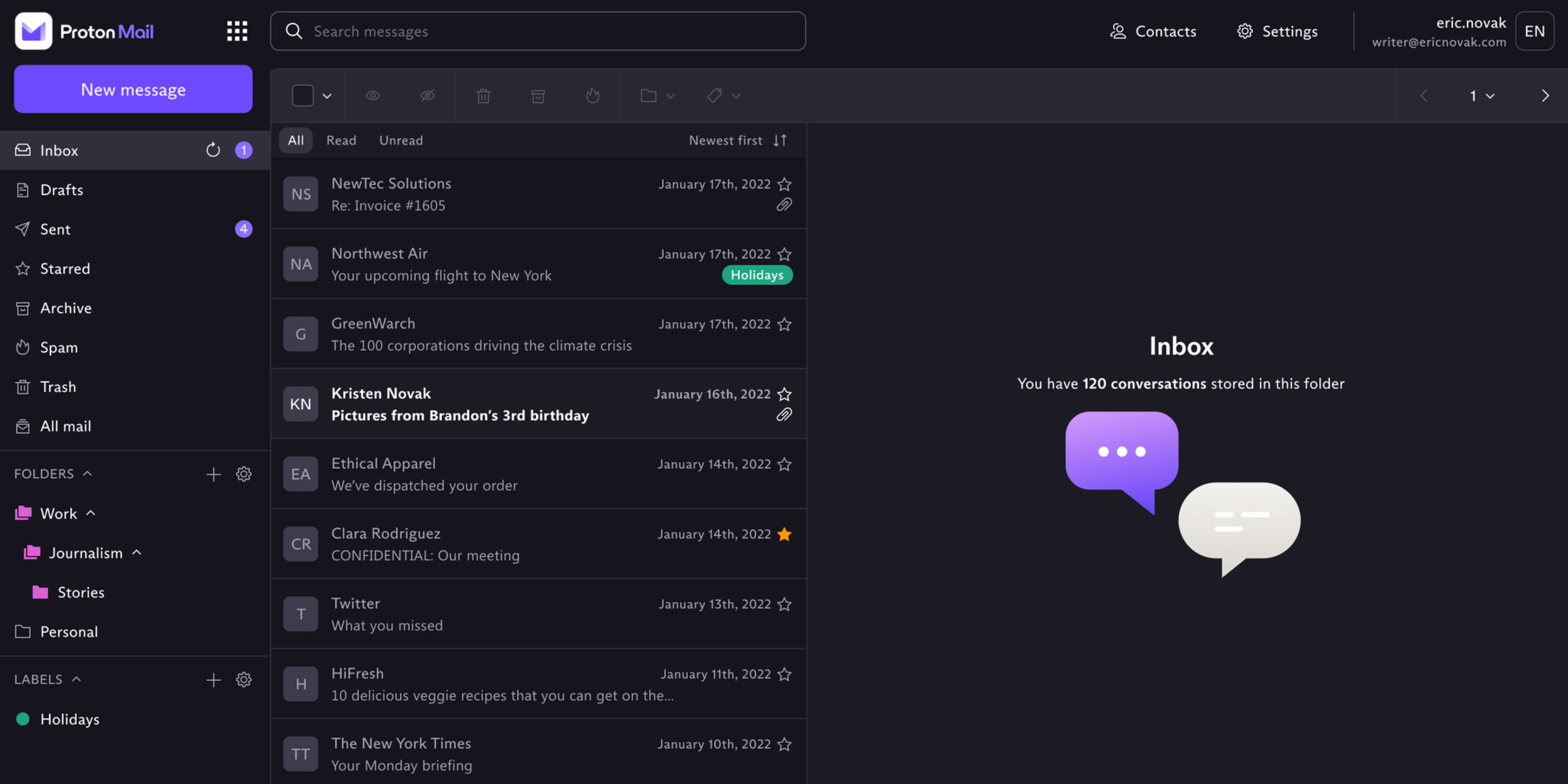
Proton Business Suite Review 2026
Independent 2026 review of Proton Business Suite covering fit, security controls, pricing, migration planning, and competitive tradeoffs.

UGREEN vs Synology NAS (2026)
Practical SMB comparison of UGREEN NASync and Synology DiskStation with verified specs, software tradeoffs, and total ownership context.

Black Friday Cybersecurity Deals Playbook (2026)
Practical Black Friday cybersecurity buying framework for SMB teams and operators: what to buy, what to avoid, and how to validate pricing and claims before purchase.