Quick Overview
- Audience: IT/security leaders and operations teams planning collaboration-platform migration
- Intent type: Implementation guide and migration planning framework
- Primary sources reviewed: Proton business documentation, NIST CSF 2.0, migration operations guidance
- Migration timeline: 4-8 weeks for typical 50-person organization
- Key considerations: SSO/identity provider replacement, MDM replacement if using Google Endpoint Management, potential hardware refresh for Chromebook fleets
Last updated: March 2, 2026
This guide provides a practical framework for organizations evaluating alternatives to Google Workspace. It covers dependency mapping, platform alternatives (managed and self-hosted), identity provider transition, device management replacement, migration complexity assessment, and post-cutover governance requirements.
Organizations typically pursue this migration to achieve zero-access data architecture, meet client data sovereignty requirements, or simplify compliance documentation under privacy-heavy regulatory frameworks. The process requires careful planning across email, identity, device management, and physical hardware dependencies.
Why are businesses leaving Google Workspace?
Businesses leave Google Workspace to reduce legal exposure, meet strict client data sovereignty requirements, and prevent provider-level access to sensitive data.
Data Access And Business Model Tension
Google Workspace is operated by a company whose broader business model is built around data-driven services. Even with enterprise controls, some organizations prefer zero-access architecture where the provider cannot access stored communications and documents, even with legal compulsion.
Regulatory And Jurisdiction Complexity
Teams subject to GDPR, HIPAA, or sector-specific controls often face additional legal and documentation overhead when data flows through globally distributed U.S.-based infrastructure.
Client Trust And Data Sovereignty
Professional services, healthcare, legal, and financial firms increasingly encounter client requirements for privacy-first infrastructure and demonstrable jurisdictional controls over data storage and access.
How to audit Google Workspace dependencies before migration
Map all operational dependencies across email, cloud storage, and third-party API integrations before initiating a platform migration.
Before changing any platform, catalog your real operational dependencies by business process rather than just the application level.
Core Systems To Inventory
Document current usage patterns and dependencies for each core system:
- Email: mailbox sizes, shared addresses, filters, routing, and third-party connectors
- Drive: storage volume, sharing models, external access, and offline workflows
- Docs/Sheets/Slides: real-time collaboration intensity and template dependencies
- Calendar/Meet: scheduling workflows, integrations, and recording/transcription needs
Integration Mapping
Document all API and workflow dependencies first:
- CRM and support systems connected to Gmail
- Automation tools tied to Drive or Calendar
- SSO/authentication dependencies on Google identity (see dedicated section below)
- Email security tools and spam filtering integrations
- Backup solutions that sync with Google Drive
- Google Voice phone system and call routing
- Google Meet hardware in conference rooms (Logitech, Asus, Lenovo devices)
Dependency Audit
Catalog usage by business process, not only by app. Prioritize systems that can disrupt revenue, client delivery, or compliance if moved incorrectly.
Pilot Design
Select a representative pilot group, migrate with parallel access, then log every friction point and required workaround.
Phased Rollout
Migrate by function or department in controlled waves, with support playbooks and communication templates ready.
Stabilize And Optimize
Validate delivery, permissions, and integrations; then retire legacy Google dependencies on a documented schedule.
What are the best privacy-first alternatives to Google Workspace?
Proton Business Suite and self-hosted platforms like Nextcloud offer the most direct alternatives featuring zero-access or full-control architecture.
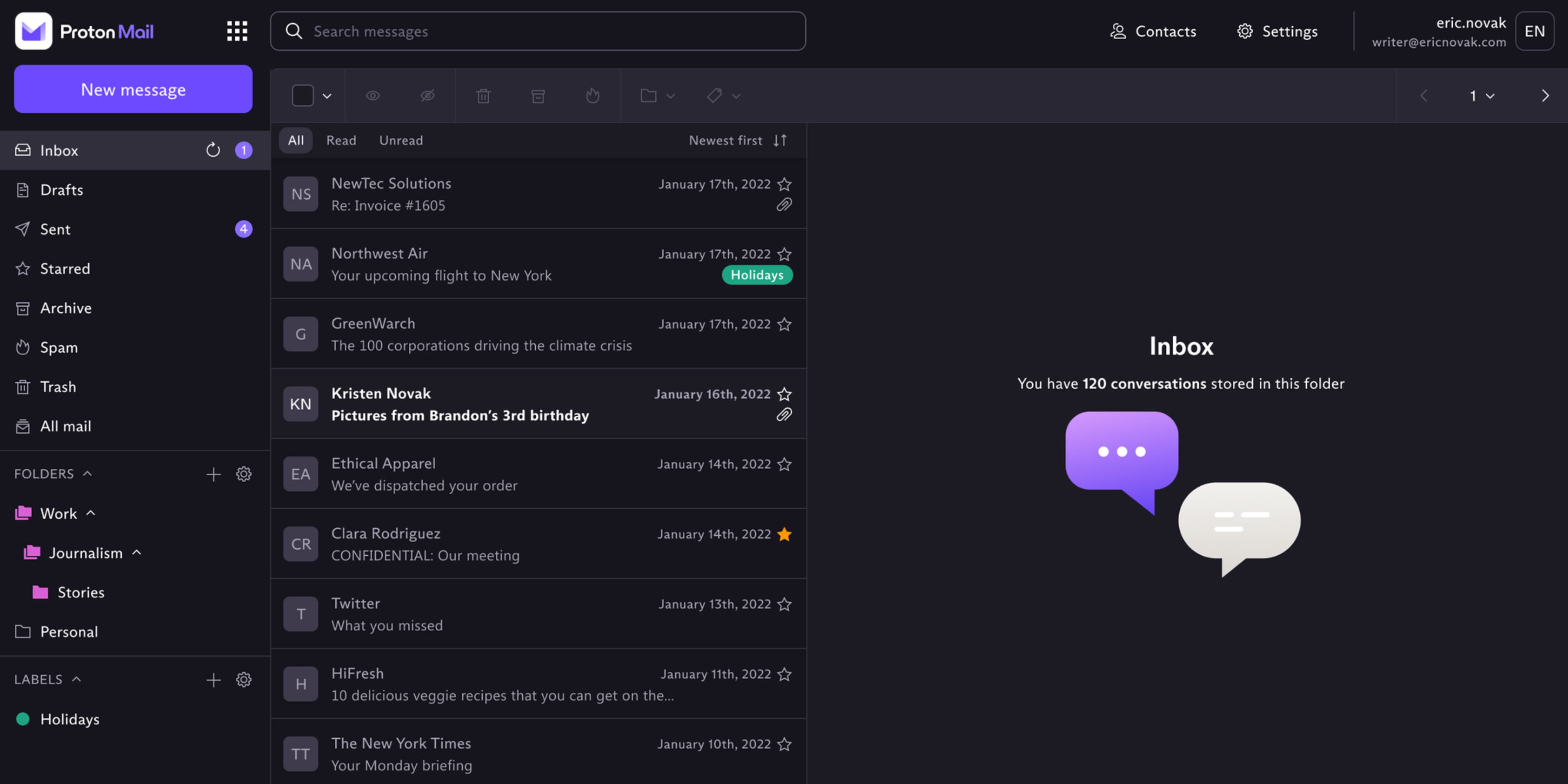
For teams requiring an out-of-the-box managed solution, Proton Business Suite is the most direct consolidated alternative.
Core Platform Components
Proton Business Suite consolidates email, calendar, storage, VPN, and password management under a unified zero-access architecture. The platform includes custom domain support, migration tooling, and cross-platform clients (Windows, macOS, iOS, Android, Linux). For detailed operational analysis, see the Proton Business Suite Review.
Managed SaaS vs Self-Hosted: Proton vs Nextcloud
Organizations evaluating Google alternatives typically choose between a managed, privacy-first SaaS platform or a self-hosted open-source stack.
Proton Business Suite (Managed SaaS):
- Zero-access encrypted infrastructure maintained by Proton
- No internal infrastructure or Linux administration required
- Automatic security updates and platform maintenance
- Swiss jurisdiction with hardware sovereignty model
- $12.99/user/month for the full business suite
Nextcloud (Self-Hosted Open Source):
- Complete control over infrastructure, data location, and access policies
- Requires dedicated server infrastructure and Linux/DevOps skills
- Self-managed security updates, backup strategy, and monitoring
- Total infrastructure control including hardware location choice
- Infrastructure costs typically $200-600/month for 20-50 users plus internal labor
When to choose Proton: Teams that prioritize operational simplicity, need immediate migration capability, and want provider-managed security without infrastructure overhead. See the Proton Business Suite Review for detailed operational analysis.
When to choose Nextcloud: Organizations with existing infrastructure expertise, hard requirements for on-premise hosting, or regulatory mandates preventing any third-party data custody.
For most SMB and mid-market teams, Proton's managed model eliminates the operational burden of self-hosting while still achieving zero-access architecture. Organizations with dedicated infrastructure teams and strict on-premise requirements should evaluate Nextcloud or similar self-hosted platforms.
| Factor | Proton Business Suite | Nextcloud (Self-Hosted) |
|---|---|---|
| Infrastructure management | Provider-managed | Self-managed (requires Linux/DevOps) |
| Setup timeline | 1-2 days for basic deployment | 1-2 weeks including infrastructure setup |
| Security updates | Automatic | Manual (requires ongoing maintenance) |
| Cost model (20-50 users) | $12.99/user/month (predictable) | $200-600/month infrastructure + labor |
| Data sovereignty | Swiss jurisdiction, zero-access | Complete control, your infrastructure |
Pricing Context (20 Users, Annual)
For a detailed feature-by-feature comparison, see Google Workspace vs Proton Mail Business.
| Platform | Base Subscription | Likely Add-Ons | Total Estimated Annual Cost |
|---|---|---|---|
| Google Workspace Stack | $3,360 | Estimated Third-Party Security Add-ons ($1,600-$4,200) | $4,960-$7,560 |
| Proton Business Suite | $3,118 | Optional video stack ($0-$2,000) | $3,118-$5,118 |
Migration Success Story
"The migration itself took 6 weeks for our 42-person team, but the compliance benefit was immediate. We eliminated provider-access concerns from client security questionnaires entirely, which directly accelerated two enterprise procurement cycles that had stalled on data-handling questions." — IT Director, legal services firm (anonymized), migrated Q4 2025
Calculate your migration cost and timeline
Map your current Google dependencies and receive a customized migration roadmap with effort estimates.
Start AssessmentHow to replace Google as your identity provider (SSO)
Replace Google SSO with Microsoft Entra ID, Okta, password manager SAML capabilities, or maintain hybrid Google identity licensing while migrating productivity workloads.
Organizations using "Sign in with Google" as their identity provider for third-party applications face a critical dependency that extends beyond email and productivity tools.
Common SSO Dependencies
Many businesses use Google as the authentication gateway for:
- SaaS applications: Slack, Zoom, Asana, monday.com, CRM platforms, helpdesk systems
- Development tools: GitHub, GitLab, cloud infrastructure consoles (AWS, GCP, Azure)
- Marketing platforms: Analytics tools, advertising platforms, social media management
- HR and finance systems: Payroll, expense management, applicant tracking systems
When you migrate away from Google Workspace, these "Sign in with Google" connections break unless you maintain a hybrid model or transition to a replacement identity provider.
Identity Provider Replacement Strategies
Option 1: Microsoft Entra ID (formerly Azure AD)
- Included with Microsoft 365 Business Premium or standalone
- Supports SAML, OAuth, OpenID Connect for broad application compatibility
- Natural fit if you're adopting Microsoft 365 alongside Proton for email
- Cost: Included in M365 plans or $6-9/user/month standalone
Option 2: Okta
- Dedicated enterprise identity platform with extensive application catalog
- Supports 7,000+ pre-built integrations
- Premium option for organizations prioritizing identity as core infrastructure
- Cost: Starting at $2-5/user/month for Workforce Identity Cloud
Option 3: Password Manager SSO (Proton Pass, 1Password, Bitwarden)
- Modern password managers offer SAML/SCIM capabilities for identity management
- Proton Pass Professional includes SAML SSO and SCIM provisioning ($6.99/user/month)
- Best for smaller organizations (under 100 users) with straightforward SSO needs
- See password manager comparison for detailed feature analysis
Option 4: Hybrid Model (Maintain Google for Identity Only)
- Retain Google Workspace at the Business Starter tier ($6/user/month)
- Use Google solely for SSO/authentication, migrate email/productivity to Proton
- Minimizes disruption to existing integrations
- Total cost still lower than full Google stack with security add-ons
Migration Approach for SSO Dependencies
Organizations should inventory all "Sign in with Google" integrations before cutover:
- Audit phase: Document every SaaS application using Google authentication
- Categorize by criticality: Identify systems that would block core operations if authentication breaks
- Test IdP transition: Validate new authentication method in pilot before production cutover
- Plan user re-authentication: Budget 5-10 minutes per user to reconnect critical applications post-migration
- Maintain fallback period: Keep both identity systems active for 2-4 weeks during transition
SSO migration timeline
Organizations with 15+ applications using Google SSO should budget an additional 2-4 weeks for identity provider transition and application reconnection testing. This is separate from the email migration timeline.
What are the most common Google Workspace migration challenges?
Large mailbox migrations, third-party integration failures, and shared mailbox workflow redesigns represent the highest-frequency migration blockers.
Typical Issues
- Large mailbox migrations can take 3-7 days for users with 50GB+ mailboxes, depending on bandwidth and API throttling
- Shared mailbox workflows may need redesign (approximately 15-20% of organizations use shared mailboxes heavily)
- Gmail-specific third-party integrations require replacement patterns (CRM connectors, helpdesk routing, automation tools)
- Calendar and search behavior changes need user retraining (budget 2-3 training sessions per department)
Practical Mitigations
- Migrate high-volume users earlier
- Implement documented forwarding/alias workflows for shared addresses
- Build an integration remediation list before cutover
- Train users on new search, labeling, and collaboration patterns
Mobile app and physical hardware considerations
Mobile workflows: Users accustomed to Google Drive and Docs mobile apps will need to adapt to Proton Drive or Nextcloud mobile applications for offline document access. Budget additional training time for mobile-first users.
Conference room hardware: Organizations using Google Meet hardware (Logitech, Asus, or Lenovo devices certified for Google Workspace) will need to replace or repurpose these units. Modern alternatives include Zoom Rooms hardware or Microsoft Teams-certified devices.
Google Voice: Businesses using Google Voice for VoIP need a complete telephony migration to platforms like RingCentral, Dialpad, or traditional business VoIP providers. This represents a separate telecom project with its own timeline and complexity.
How to replace Google Endpoint Management and device controls
Organizations using Google Workspace's built-in Mobile Device Management (MDM) or Google Endpoint Management to manage company devices face an additional migration layer beyond email and productivity tools.
Windows / Mixed Fleet
Apple Heavy Fleet
Chromebooks
For comprehensive endpoint security considerations, see the Endpoint Protection Guide.
Device Management Replacement Options
Microsoft Intune (included with Microsoft 365 Business Premium or standalone)
- Manages Windows, macOS, iOS, and Android devices
- Policy enforcement, remote wipe, conditional access controls
- Native integration if you're already in the Microsoft ecosystem
- Cost: Included in M365 Business Premium ($22/user/month) or $8/user/month standalone
Jamf Pro (macOS and iOS specialist)
- Premium MDM for Apple device fleets
- Deep macOS policy control and automation
- Primarily for organizations with >50% Apple hardware
- Cost: Quote-based, typically $5-8/device/month
Kandji (modern Apple MDM)
- Cloud-native MDM focused on macOS and iOS
- Automated device compliance and zero-touch deployment
- Ideal for remote-first teams with Apple hardware
- Cost: Starting at $6/device/month
Android and Chromebook Hardware Dependencies
Organizations heavily invested in Google hardware face additional migration complexity. For broader mobile security considerations, see the Mobile Workforce Security Guide.
Android Enterprise (company phones/tablets):
- If managed via Google Workspace, devices must be re-enrolled in a new MDM platform
- Consider migrating to Intune (supports Android Enterprise), Jamf, or a dedicated Android MDM
- Budget 15-30 minutes per device for re-enrollment unless using zero-touch provisioning
Chromebook fleets:
- Chromebooks are tightly coupled to Google Workspace for management and authentication
- Replacement requires either continuing lightweight Google Workspace licensing for device management only, or full hardware refresh to Windows/macOS
- For organizations with 20+ Chromebooks, hardware replacement represents a significant capital expense ($400-800 per device)
Practical migration approaches:
- Hybrid model: Retain Google Workspace at a lower tier (Business Starter at $6/user/month) solely for Chromebook/Android management, while migrating email/productivity to Proton
- Hardware transition: Phase out Chromebooks during normal refresh cycles; manage replacement Windows/macOS devices via Microsoft Intune or Jamf
- Complete MDM migration: Re-enroll Android devices in Microsoft Intune or equivalent, retire Chromebooks, accept one-time disruption cost
Hardware migration complexity
Organizations with >30% Chromebook deployment or Android Enterprise fleets should budget an additional 4-8 weeks for device management migration and potential hardware transition planning.
What are the key readiness gates before migration cutover?
Validate identity continuity, email routing stability, collaboration workload readiness, integration continuity, and support preparedness before production cutover.
Teams should not cut over based on calendar pressure alone. Use explicit readiness gates so operations, security, and leadership all agree on launch conditions.
| Readiness gate | Pass criteria | Common blocker |
|---|---|---|
| Identity and access continuity | Admin roles, MFA policies, offboarding workflows, and SSO integrations validated on target platform | Third-party applications still require Google SSO without replacement IdP tested |
| Email and routing stability | Pilot users receiving/sending reliably with tested forwarding and alias behavior | Undocumented shared mailbox behavior and routing edge cases |
| Collaboration workload validation | Critical documents/calendars tested by real users in target departments | Template and workflow assumptions not validated in pilot |
| Integration continuity | CRM/helpdesk/automation connectors mapped and remediated | Late discovery of API dependencies at cutover week |
| Support readiness | User comms plan, internal support scripts, escalation owner list published | No defined owner for cutover-day triage |
Pilot validation required
If pilot users cannot complete core work reliably, defer production cutover until workflow stability is validated. Premature migration typically increases downtime and reduces user trust.
What downtime should IT teams expect during email cutover?
Properly planned migrations achieve zero email downtime through dual-delivery configuration, with DNS propagation completing in 2-4 hours and MX validation requiring 24-48 hour monitoring.
DNS and MX Record Cutover Windows
DNS Propagation Timeline:
- Typical propagation: 2-4 hours for most resolvers
- Maximum propagation: 24 hours for global reach including slow-updating resolvers
- Recommendation: Execute DNS changes during low-traffic periods (Friday evening or weekend) to minimize business impact
MX Record Transition:
- Dual-delivery monitoring window: 24-48 hours required
- During this period, configure both Google and Proton MX records with different priorities
- Monitor both inboxes to ensure no mail loss during DNS propagation
- SPF/DKIM/DMARC validation: 2-4 hours after DNS propagation completes
Expected Service Continuity:
- Email delivery: Zero downtime with proper dual-delivery configuration
- Calendar access: Continuous (no DNS dependency for existing authenticated users)
- Drive/storage: Continuous (migration happens separately from DNS cutover)
- Authentication: Brief 1-2 minute interruption during SSO configuration updates
Resource Requirements for IT Teams
Organizations should budget the following IT administrator time during active migration:
- Planning phase (weeks 1-2): 8-12 hours total for dependency mapping and pilot design
- Pilot phase (weeks 3-4): 2-3 hours per week for monitoring and issue triage
- Cutover phase (week 5): 6-10 hours concentrated during cutover weekend/week
- Stabilization phase (weeks 6-8): 2-3 hours per week for user support and integration validation
For a 50-person organization, total IT effort typically ranges from 30-50 hours across an 8-week migration program.
For detailed guidance on pilot design and phased rollout strategies, see the Small Business Cybersecurity Roadmap for structured implementation frameworks.
How does migration improve compliance posture?
Swiss jurisdiction and zero-access architecture provide hardware sovereignty advantages that can simplify evidence and controls for privacy-heavy regulatory frameworks.
Proton's zero-access encryption protects stored data and message bodies. Note that subject lines in unencrypted inbound emails from non-Proton senders pass through servers momentarily before encryption—this is an industry-standard SMTP limitation, not specific to Proton.
- GDPR: Stronger data-minimization posture through zero-access storage and hardware sovereignty under Swiss jurisdiction
- HIPAA: Stronger technical safeguards and provider-access reduction at the encryption layer
- Client confidentiality: Better alignment for legal/financial/professional service models requiring demonstrable data isolation
While the US-EU Data Privacy Framework also covers Google Workspace, Proton's Swiss jurisdiction combined with zero-access architecture offers hardware sovereignty—no provider staff can access stored content, even under legal compulsion.
When should organizations delay migration?
Delay migration if critical dependencies remain unmapped, no internal migration owner exists, or the business is undergoing concurrent major operational changes.
Some organizations should defer migration until prerequisites are in place. Premature migration can create avoidable operational disruption and control gaps.
| Condition | Why migration should wait | Prerequisite to proceed |
|---|---|---|
| No dependency map for email/calendar integrations | Hidden dependencies will surface during cutover and disrupt operations | Complete integration inventory and remediation plan |
| No internal owner for migration operations | Escalation and support decisions become inconsistent | Named program owner and cross-functional support roster |
| High-change period in business operations | Concurrent major changes increase failure and adoption risk | Dedicated migration window and stabilized operational calendar |
What should teams focus on in the first 30 days after migration?
Stabilize delivery and permissions in week 1, validate security controls in week 2, remove legacy fallback paths in week 3, and publish outcomes in week 4.
Post-migration governance prevents users from reverting to unmanaged shadow IT. Teams that skip post-cutover controls often reintroduce legacy patterns when facing operational pressure.
Week 1: Stabilize communication and permissions
Track delivery failures, permission mismatches, and high-friction user tasks daily. Resolve with named owners and response SLAs.
Week 2: Validate security posture drift
Reconfirm MFA enforcement, role assignments, and external sharing rules after real-world usage begins.
Week 3: Remove legacy fallback risk
Decommission unnecessary Google-era forwarding, duplicate accounts, and shadow workflows that bypass the new control model.
Week 4: Publish leadership report
Summarize migration outcomes, unresolved risk items, user adoption metrics, and next-quarter hardening priorities.
Post-cutover governance metrics
| Metric | Target signal | Escalation threshold |
|---|---|---|
| Mail delivery incident rate | Declining week-over-week after cutover | Repeated delivery failures in critical workflows |
| Permission and access exceptions | Backlog reduced to low-severity residual items | Admin/finance access issues unresolved > 48 hours |
| Legacy dependency removal progress | Documented retirement of Google-only dependencies | Core workflows still dependent on unmanaged legacy paths |
Best For
- Stronger privacy posture through zero-access architecture
- Better jurisdictional control for international and regulated operations
- Integrated security stack can reduce total tool sprawl
- Clearer privacy story for client trust and procurement reviews
Consider Alternatives If
- Document collaboration depth may not match Google in all workflows
- Some integrations require redesign or replacement
- Migration needs planning, training, and temporary dual-platform overhead
- User adaptation can take 1-2 weeks with active support
Recommendation
Treat de-Googling as a program, not a project ticket. Teams that succeed define scope clearly, pilot with realistic users, and execute in phases with strong support and communication.
For detailed step-by-step migration procedures including DNS configuration and user onboarding sequences, see the Google Workspace to Proton Migration guide. To evaluate whether Proton Business Suite fits your operational requirements, read the full Proton Business Suite Review.
Compare Privacy-First Business Platforms
Use these tracked links to evaluate Proton Business Suite and related privacy-focused alternatives before migration.
Proton Business Suite
Privacy-first business productivity suite
Starting at $14.99/user/month
Google Workspace Email Security
Built-in Gmail security features
Starting at $7/user/month
Affiliate disclosure: We may earn a commission from purchases made through these links at no additional cost to you. Recommendations are based on fit and operational quality, not commission size.
Frequently Asked Questions
Related Articles
More from Migration Planning and Privacy-First Infrastructure

Google Workspace to Proton Migration
Detailed migration sequence covering DNS cutover, user onboarding, and post-migration validation.
Proton Business Suite Review
Operational and pricing review of Proton's business stack for privacy-focused organizations.

Google Workspace vs Proton Mail Business
Side-by-side comparison for teams deciding between collaboration depth and privacy model.
Primary references (verified 2026-03-02):
- Proton for Business
- Proton Mail and Easy Switch
- NIST Cybersecurity Framework 2.0 (see our NIST CSF 2.0 implementation guide)
Ready to evaluate your security stack?
Get a customized assessment that maps your privacy, compliance, and tooling priorities before migration.
Start Free Assessment