Quick Overview
- Primary use case: Build or refresh a cybersecurity program using NIST CSF 2.0 without overengineering
- Audience: SMB owners, finance/operations leaders, and IT/security managers
- Intent type: Implementation guide
- Primary sources reviewed: NIST CSWP 29, NIST SP 1299/SP 1300/SP 1301, FTC SMB guidance, CISA SMB guidance
Last updated: February 19, 2026
Key Takeaway
NIST CSF 2.0 works best as an operating cadence, not a documentation project: define ownership, scope a realistic profile, execute a 90-day baseline, and review evidence quarterly.
NIST Cybersecurity Framework (CSF) 2.0 gives teams a common structure for managing cybersecurity risk, but structure alone does not reduce incidents. Execution does. This guide focuses on turning the framework into a practical operating model for small and mid-sized organizations—with clear owners, measurable controls, and governance routines that leadership can actually run.
If you need a baseline before rollout, start with the NIST CSF 2.0 Assessment Tool, then map emerging threats with the AI Cyberattacks and NIST Guide.
What is NIST CSF 2.0 and what changed from version 1.1?
NIST CSF 2.0 is the updated federal cybersecurity framework that introduces "Govern" as a sixth core function to explicitly manage organizational risk.
Definition: A CSF 2.0 implementation is a repeatable risk-management cycle where each function has a named owner, required evidence, and a review cadence.
Published on February 26, 2024 as CSWP 29, the framework is designed for organizations of all sizes, sectors, and maturity levels. The most critical structural change from version 1.1 is the addition of the Govern function, joining Identify, Protect, Detect, Respond, and Recover. This elevates governance from an implicit expectation to a foundational requirement. Risk appetite, policy ownership, oversight cadence, and supply-chain risk treatment are now explicit components of the framework core.
Why does NIST CSF 2.0 matter for SMB and mid-market teams in 2026?
CSF 2.0 provides lean security teams with a free, flexible operating model to prioritize controls, manage risk, and generate audit evidence.
SMB and mid-market teams face the challenge of running disciplined security programs with limited staff. Rather than forcing a heavy compliance platform, CSF 2.0 offers a shared decision framework between leadership and technical teams. Both the FTC and CISA endorse the framework because it improves outcomes by splitting responsibility across leadership, program management, and IT execution. Using CSF 2.0 allows teams to prioritize controls in phases and generate the exact evidence required to support customer, audit, or insurance conversations.
If you need to establish your baseline before rolling out these phases, the free Valydex Assessment provides an immediate current-state profile.
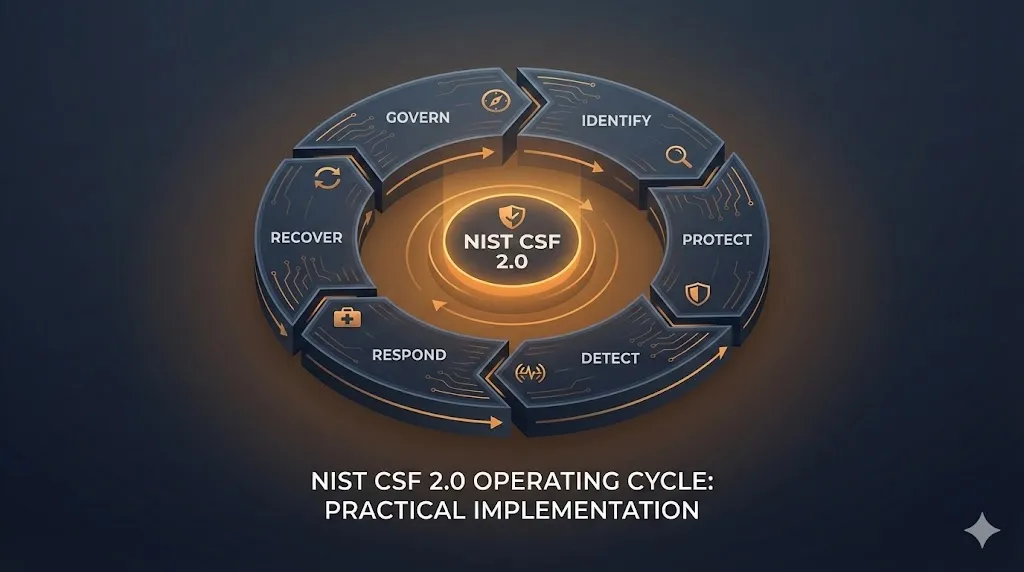
The Six Functions as an Operating Cycle
Treat the six functions as a loop that runs continuously. Each function should answer one decision question and produce visible evidence.
| Function | Core question | Practical owner | Minimum evidence |
|---|---|---|---|
| Govern | How do we define risk decisions and accountability? | Executive sponsor + program owner | Policy set, risk register, quarterly review notes |
| Identify | What assets, data, and dependencies matter most? | Security program manager + IT | Asset inventory, critical-system map, dependency list |
| Protect | Which safeguards reduce likely and high-impact failure modes? | IT/security lead | MFA coverage, patch status, backup configuration evidence |
| Detect | How do we know quickly when controls fail? | IT/security lead | Alert runbooks, log coverage map, detection tuning records |
| Respond | Who does what in the first hours of an incident? | Program manager + incident lead | Incident response plan, contact tree, tabletop outputs |
| Recover | How fast can we restore critical operations safely? | Operations + IT + leadership | Restore-test records, communications plan, corrective actions |
When this table is in place and updated, framework adoption becomes concrete: leaders can see risk tradeoffs, and operators can see what "done" means.
Role mapping that keeps implementation moving
A frequent issue is assigning "security" to one technical owner without distributing accountability. For smaller teams, assign roles by function rather than department size:
- Executive sponsor (CEO/COO/CFO): approves risk posture, resolves blockers, and accepts residual risk.
- Security program owner: maintains roadmap, coordinates owners, and reports progress.
- IT/security lead: implements and verifies technical controls.
- Operations/finance owner: validates process controls for payments, onboarding, and business continuity.
- Compliance/legal support (if present): aligns policy wording and contractual obligations.
One person can hold multiple roles in smaller organizations, but each role still needs explicit accountability in writing.
In a 50-person company, the CEO often serves as executive sponsor, risk owner, and de facto compliance lead simultaneously. This is workable provided the Govern function is treated as a recurring calendar commitment rather than a title. A practical approach: schedule a 60-minute quarterly review with whoever owns the risk register, document decisions and accepted risks in writing, and keep the policy set short enough that one person can actually maintain it. The goal is a defensible record of deliberate risk decisions—not a governance structure that requires a dedicated compliance team to sustain.
How to Scope Your First CSF 2.0 Profile
Scope your first CSF 2.0 profile by targeting a single, business-critical system boundary and defining target outcomes achievable within 90 days.
NIST SP 1301 defines profiles as a way to express current and target cybersecurity outcomes. To avoid stalling your implementation, start with a narrow boundary around workflows that create the largest business impact if disrupted—such as identity management, email, or payment systems. Document your current outcomes using evidence-backed statements, avoiding policy language that cannot be proven in logs or test records. Next, choose a target set of improvements that reduce the likelihood of compromise and assign them a specific owner and due date. If your profile grows faster than your ability to execute, reduce the scope immediately.
How-To: First Profile in 30 Days
Set a narrow boundary
Define the initial scope around the systems and workflows that create the largest business impact if disrupted. Common starting points are identity, email, endpoint fleet, and payment-critical systems.
Capture current outcomes
For each function, document what is currently true using short, evidence-backed statements. Avoid policy language that cannot be demonstrated in logs, tickets, or test records.
Define target outcomes
Choose a small target set that can be executed in 90 days. Prioritize outcomes that reduce likelihood of account compromise and improve restoration confidence.
Prioritize by risk and effort
Rank gaps by business impact and implementation effort. Mark each item with owner, due date, and escalation trigger.
A scoped profile is successful when it guides action. Complete one full cycle before expanding scope.
Maturity vs. Compliance: Tiers and Profiles
Profiles define what outcomes you are implementing now versus next. Tiers describe how rigorous your governance and risk-management approach is over time. NIST defines four CSF Tiers in its CSF Tier glossary entry: Partial (Tier 1), Risk Informed (Tier 2), Repeatable (Tier 3), and Adaptive (Tier 4). For most SMB teams, start by building one usable current/target profile first, then use tiers to track maturity progression quarter by quarter.
Accounting for employee AI tool use under Govern and Identify
For 2026 implementations, the Govern and Identify functions should explicitly address how employees use AI tools in their daily work. Unauthorized use of tools like ChatGPT, Copilot, or other generative AI services—sometimes called Shadow AI—can expose sensitive business data to third-party model training pipelines without IT visibility.
Under Govern, this means adding an acceptable-use policy for AI tools that defines which services are approved, what data categories may not be submitted to external AI systems, and who is responsible for reviewing new tool requests. Under Identify, it means including AI-connected applications in your asset and data-flow inventory, even if they are browser-based and not formally procured. A practical starting point is a short employee survey asking which AI tools are currently in use, followed by a policy decision on each.
Where should teams pull controls and templates from?
NIST provides structured resources that remove the need to build from a blank spreadsheet.
- CSF 2.0 Quick Start Guides: Targeted guides for Profiles, Small Business, Tiers, and Enterprise Risk Management — a practical starting point for most teams.
- Community Profiles guidance: Check whether your sector has shared implementation priorities you can reuse rather than building your baseline from scratch.
- NIST Cybersecurity and Privacy Reference Tool (CPRT): Searchable, downloadable reference data (XLSX/JSON) for operationalizing controls in tickets, spreadsheets, or governance tooling.
Control Baseline by Function
For teams that need a practical starting point, this baseline maps each function to a minimum control set.
| Function | Baseline control set | Execution note |
|---|---|---|
| Govern | Written policy baseline, risk register, quarterly governance meeting | Keep policy set short and owner-specific |
| Identify | Asset inventory, critical data map, third-party dependency list | Include cloud services and unmanaged edge cases |
| Protect | MFA coverage, secure configuration standards, patch cadence, backup policy | Track exception inventory, not just policy status |
| Detect | Centralized log collection for critical systems, alert triage workflow | Tune alerts to reduce noise and missed escalation |
| Respond | Incident response runbook with decision authority and contacts | Test with role-based tabletop scenarios |
| Recover | Recovery priorities, restore testing schedule, customer/internal comms plan | Measure restoration time against business tolerance |
This baseline aligns with the quick-start intent in NIST SP 1300 for smaller organizations with modest or early-stage programs.
For leadership visibility, pair this table with a one-page critical-asset and dependency map in your quarterly review packet. It gives non-technical stakeholders a faster view of where disruption risk concentrates.
Evidence-first rule
For each baseline control, decide the evidence artifact before rollout starts. Example evidence types:
- MFA: Export of conditional access policies from Microsoft Entra ID and per-user MFA status report; exception aging report for any bypassed accounts
- Endpoint protection: EDR coverage report from Microsoft Defender for Business, CrowdStrike Falcon Go, or equivalent showing enrolled vs. unmanaged devices
- Patching: Median and P90 remediation time for high-severity findings from your patch management or vulnerability scanner (e.g., Tenable Nessus)
- Backups: Restoration test results against production-like systems with documented recovery time
- Incident response: Tabletop exercise outputs with named owners, identified gaps, and closure dates
If evidence cannot be produced on demand, treat the control as partially implemented.
What tools satisfy the Detect and Protect functions on a budget?
SMB and mid-market teams can satisfy the Detect and Protect functions using a focused stack of category-leading tools without enterprise-scale spend.
| Function | Tool category | Budget-range examples |
|---|---|---|
| Protect – Identity | MFA / SSO | Microsoft Entra ID P1, Okta Workforce Identity |
| Protect – Endpoint | EDR / antivirus | Microsoft Defender for Business, Bitdefender GravityZone, ESET PROTECT Essential |
| Protect – Device management | MDM | Microsoft Intune, Jamf Pro, Kandji |
| Protect – Email | Email security gateway | Microsoft Defender for Office 365, Proofpoint Essentials |
| Detect – Log aggregation | SIEM / log management | Microsoft Sentinel (consumption-based), Elastic SIEM, Datadog Cloud SIEM |
| Recover – Backup | Backup and recovery | Acronis Cyber Protect, IDrive Business, Azure Backup |
You do not need every category on day one. Prioritize identity (MFA + SSO), endpoint (EDR), and backup before expanding to SIEM. A focused stack with consistent coverage is more effective than a broad one with gaps.
For vulnerability scanning and patch tracking, Tenable Nessus Essentials offers a free tier that works well for smaller environments getting started with the Identify function.
Not sure which tools fit your current maturity?
Run the free Valydex Assessment to get a prioritized tool and control recommendation based on your team size and risk profile.
Start Free Assessment90-Day Implementation Plan
A 90-day cycle is enough to establish control ownership and governance rhythm without forcing large platform migrations.

Days 1–30: Baseline and accountability
- Appoint executive sponsor and program owner
- Lock initial scope boundary for first profile cycle
- Build initial asset/dependency inventory
- Document current-state outcomes for all six functions
- Identify top five risk gaps with named owners
Days 31–60: Control execution
- Close MFA coverage gaps on workforce and privileged access
- Enforce patching cadence with exception workflow
- Validate backup strategy and run first restoration test
- Formalize detection triage and escalation routing
- Complete first tabletop incident exercise
Days 61–90: Governance and hardening
- Publish target profile and remediation plan for next quarter
- Run third-party control review on critical vendors
- Measure and report baseline metrics to leadership
- Close high-priority corrective actions from tabletop and restore tests
- Update policy language based on operational feedback
By day 90, the goal is a repeatable program state: owners are known, evidence exists, and unresolved risks are visible to leadership. For a more detailed 90-day rollout sequence, see the Small Business Cybersecurity Roadmap.
Not sure where your program stands today?
Run the free Valydex Assessment to get a current-state snapshot across all six CSF functions before you start your 90-day cycle.
Start Free AssessmentWhat does NIST CSF 2.0 implementation cost?
For most SMB and mid-market teams, the primary cost of NIST CSF 2.0 implementation is internal staff time—the framework itself is free.
A realistic estimate for the 90-day baseline plan:
| Role | Estimated hours (90 days) | Primary activities |
|---|---|---|
| Security program owner | 40–60 hours | Scoping, coordination, documentation, reporting |
| IT / security lead | 60–80 hours | Control implementation, evidence collection, testing |
| Executive sponsor | 8–12 hours | Risk decisions, policy approvals, quarterly review |
| Operations / finance owner | 10–15 hours | Process controls, vendor review, continuity planning |
Total internal investment: approximately 120–165 hours across the team for a first 90-day cycle. This is roughly equivalent to one part-time FTE for a quarter.
Tooling costs depend heavily on your existing stack:
- If your organization already uses Microsoft 365 Business Premium, most Protect and Detect controls are available within that license.
- Incremental tooling for teams starting from scratch typically runs $15–$40 per user per month for a complete SMB stack (MDM + EDR + email security + backup).
- GRC or risk-register tooling is optional for the first cycle; a structured spreadsheet is sufficient.
The largest hidden cost is remediation time for control gaps discovered during the baseline—budget an additional 20–40 hours for IT execution if significant gaps exist in MFA coverage, patching, or backup configuration.
For a deeper look at backup costs and options, see the Business Backup Solutions Guide.
Vendor and Third-Party Governance Standard
CSF 2.0 programs frequently stall at supplier boundaries. A concise third-party governance standard keeps third-party risk visible.
Minimum checks for critical vendors:
- documented data flow and storage locations
- privileged-access control model and logging coverage
- incident notification expectations in contract language
- subprocessor transparency and change notification process
- retention/deletion commitments and practical execution path
- restore and business-continuity expectations for critical services
Run these checks at onboarding and renewal. If a vendor cannot answer precisely, classify the relationship as high risk until remediation is complete.
Which metrics should leadership review each quarter?
Leadership should review a short scorecard that drives decisions, not a large dashboard that hides ownership.
Use this minimum quarterly set:
| Metric | Why it matters | Decision trigger |
|---|---|---|
| MFA coverage (workforce/admin separately) | Identity compromise risk concentration | Any privileged-access exception older than policy threshold |
| Critical patch latency | Exposure window to known vulnerabilities | Repeated threshold breach for high-severity items |
| Backup restore success on critical systems | Recovery confidence under disruption | Failed restore on priority systems |
| Incident readiness cadence | Response quality and coordination reliability | Tabletop gaps not remediated before next cycle |
| Third-party review completion | Supply-chain risk visibility | Critical vendor without current review |
| Open high-risk items aging | Program execution health | High-risk issue unresolved across two cycles |
Quarterly review outputs should always include: accepted risks, funded mitigations, deferred items with owner rationale, and next-cycle priorities.
Common Rollout Mistakes
Most CSF 2.0 challenges are implementation discipline issues, not framework problems.
| Mistake | Impact | Correction |
|---|---|---|
| Starting with broad enterprise scope | Program stalls before evidence exists | Start with one scoped profile and one 90-day cycle |
| Treating policy as proof | Control confidence is overstated | Define evidence artifacts before rollout |
| Assigning security to IT only | Governance and process gaps persist | Map accountability across leadership, program, and IT |
| Tracking too many KPIs | Signal is diluted | Keep scorecard focused on 5-7 operational metrics |
| Skipping third-party reviews | Supplier risk remains unmanaged | Gate onboarding/renewal on minimum due diligence |
If the program feels too heavy, the fix is usually tighter scoping, not more tooling.
Is NIST CSF 2.0 mandatory?
For most organizations, CSF 2.0 is a voluntary framework, not a universal legal mandate. That is also how FTC frames it for small businesses: free, flexible, and adaptable.
However, specific contractual, sector, or regulatory contexts may require controls that map closely to CSF outcomes. The practical approach is to treat CSF as the operating model, then map your specific obligations on top of it.
This avoids two extremes:
- treating CSF as optional guidance with no accountability
- treating CSF as a rigid checklist disconnected from your business risks
A practical middle path is to run the framework continuously and document where contracts, customer requirements, or regulations require tighter controls. For guidance on mapping CSF outcomes to specific compliance obligations, see the Cybersecurity Compliance Guide.
FAQ
NIST CSF 2.0 Implementation FAQs
Related Articles
More from Cybersecurity Implementation

Privacy-First Cybersecurity Guide (2026)
Build a privacy-first operating model with practical controls for data minimization, vendor governance, and incident readiness.

Small Business Cybersecurity Roadmap
A structured 90-day rollout that prioritizes high-impact controls for lean teams with limited security resources.

Cybersecurity Compliance Guide
Map your operational security controls to compliance obligations without turning your program into checkbox theater.
Affiliate note: Some links in this guide are partner links. Recommendations are based on fit and product quality, not commission rates.
Primary references (verified 2026-02-19):
Want a prioritized CSF 2.0 action plan for your team?
Run the Valydex assessment to get a practical implementation sequence aligned to your current maturity and risk profile.
Start Free Assessment